Generate All Keys Using Armstrong Axion Algorithm
Before signing the Contract.jar JAR file containing the contract file, you need to generate keys, if you don't already have suitable keys available. You need to sign your JAR file using your private key, and your recipient needs your corresponding public key to verify your signature.
- Generate All Keys Using Armstrong Axiom Algorithm Chart
- Generate All Keys Using Armstrong Axion Algorithms
- Generate All Keys Using Armstrong Axiom Algorithm 2
- Generate All Keys Using Armstrong Axiom Algorithm For Mac
This lesson assumes that you don't have a key pair yet. You are going to create a keystore named examplestanstore and create an entry with a newly generated public/private key pair (with the public key in a certificate).
Now pretend that you are Stan Smith and that you work in the legal department of Example2 corporation. Type the following in your command window to create a keystore named examplestanstore and to generate keys for Stan Smith:
The keystore tool prompts you for a keystore password, your distinguished-name information, and the key password. Following are the prompts; the bold indicates what you should type.
The preceding keytool command creates the keystore named examplestanstore in the same directory in which the command is executed (assuming that the specified keystore doesn't already exist) and assigns it the entered password. The command generates a public/private key pair for the entity whose distinguished name has a common name of Stan Smith and an organizational unit of Legal.
The self-signed certificate you have just created includes the public key and the distinguished-name information. (A self-signed certificate is one signed by the private key corresponding to the public key in the certificate.) This certificate is valid for 90 days. This is the default validity period if you don't specify a -validity option. The certificate is associated with the private key in a keystore entry referred to by the alias signLegal. The private key is assigned the password that was entered.
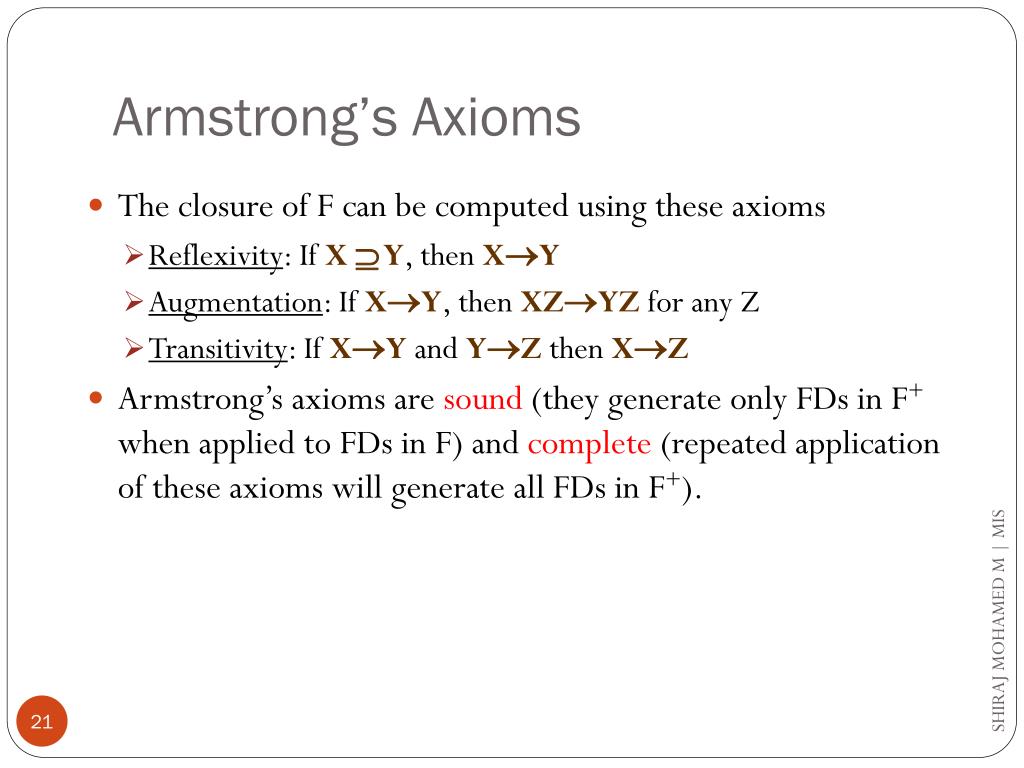
Hello every one, I want to generate all the possible key combinations for the DES algorithm 56-bit 'actuallly 64 but the last 8 bits are just padding', so can anyone plz help how can i do that? Or give me article or something that might help me?April the 1st is a couple of days away. An algorithm to map out all pages is to go the homepage, regex all form tags, add the action attribute (url) to a list, expand that action attribute list object by the request parameters in the body of the form tag (list) and also remember which request method it is (get/post). Doing this recursively, you will reach every page that you have access. Given, R and F, one can compute all candidate keys for R by exhaustively checking for all subsets of R starting from single attribute subsets. As soon as a candidate key is identifed, all its supersets need not be checked for key property as they will be superkeys. Note: If some of the attributes of R are. Is there a correct way to generate a symmetric key? That seems to be aimed to be a key generation algorithm (again speaking of Twofish). Using symmetric keys. The computer algorithm to create these keys and their format is commonly called RSA. PGP is a software encryption suite initially created in the 1990s that can perform both asymmetric encryption (such as using RSA key pairs) and symmetric encryption (which is faster or 'stronger' but less convenient).
Self-signed certificates are useful for developing and testing an application. However, users are warned that the application is signed with an untrusted certificate and asked if they want to run the application. To provide users with more confidence to run your application, use a certificate issued by a recognized certificate authority.
Key generation is the process of generating keys in cryptography. A key is used to encrypt and decrypt whatever data is being encrypted/decrypted.
A device or program used to generate keys is called a key generator or keygen.

Generation in cryptography[edit]
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender encrypts data with the receiver's public key; only the holder of the private key can decrypt this data.
Generate All Keys Using Armstrong Axiom Algorithm Chart
Generate All Keys Using Armstrong Axion Algorithms
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and SSH use a combination of the two: one party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data used to generate it). The remainder of the conversation uses a (typically faster) symmetric-key algorithm for encryption.
Computer cryptography uses integers for keys. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG). A PRNG is a computeralgorithm that produces data that appears random under analysis. PRNGs that use system entropy to seed data generally produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess. Another way to generate randomness is to utilize information outside the system. veracrypt (a disk encryption software) utilizes user mouse movements to generate unique seeds, in which users are encouraged to move their mouse sporadically. In other situations, the key is derived deterministically using a passphrase and a key derivation function.
Many modern protocols are designed to have forward secrecy, which requires generating a fresh new shared key for each session.
Classic cryptosystems invariably generate two identical keys at one end of the communication link and somehow transport one of the keys to the other end of the link.However, it simplifies key management to use Diffie–Hellman key exchange instead.
The simplest method to read encrypted data without actually decrypting it is a brute-force attack—simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer to attack, rendering a brute-force attack impractical. Currently, key lengths of 128 bits (for symmetric key algorithms) and 2048 bits (for public-key algorithms) are common.
Generation in physical layer[edit]
Wireless channels[edit]
A wireless channel is characterized by its two end users. By transmitting pilot signals, these two users can estimate the channel between them and use the channel information to generate a key which is secret only to them.[1] The common secret key for a group of users can be generated based on the channel of each pair of users.[2]
Optical fiber[edit]
A key can also be generated by exploiting the phase fluctuation in a fiber link.[clarification needed]
See also[edit]
- Distributed key generation: For some protocols, no party should be in the sole possession of the secret key. Rather, during distributed key generation, every party obtains a share of the key. A threshold of the participating parties need to cooperate to achieve a cryptographic task, such as decrypting a message.
References[edit]
Generate All Keys Using Armstrong Axiom Algorithm 2
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Feb 2016). 'Physical-Layer Secret Key Generation with Colluding Untrusted Relays'. IEEE Transactions on Wireless Communications. 15 (2): 1517–1530. doi:10.1109/TWC.2015.2491935.
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Dec 2015). 'Secret Group Key Generation in Physical Layer for Mesh Topology'. 2015 IEEE Global Communications Conference (GLOBECOM). San Diego. pp. 1–6. doi:10.1109/GLOCOM.2015.7417477.